In today’s fast paced digital international, cyber security has come to be a critical precedence for corporations of all sizes. As businesses more and more rely upon virtual structures, cloud offerings and remote paintings environments, cyber threats are growing greater state of the art and common.
From startups to international enterprises, companies are making an investment heavily in Data Protection to guard touchy facts, keep customer agree and make sure uninterrupted operations. According to enterprise reports, worldwide cybercrime cost are predicted to exceed trillion of greenback annually through 2026, making cyber safety critical rather than optionally available.
What Is Cyber Security?
Cyber security refers to the exercise of protecting structures, networks, gadgets and data from cyber attacks, unauthorized access and digital threats. It entails a aggregate of technology, approaches and pleasant practices designed to secure digital belongings.
Cyber security covers the entirety from securing personal devices to protective large organization infrastructures in opposition to hacking, malware, ransomware and records breaches.
Importance of Cyber Security in Today’s Digital World
Cyber protection performs a important function in preserving commercial enterprise continuity and digital agree with. Without proper Data Protection measures, groups face dangers such as information loss, financial damage, prison penalties and reputational harm.
Key motives cyber security is critical:
- Protects sensitive customer and business data
- Prevents economic losses from cyber attacks
- Ensures compliance with rules like GDPR and CCPA
- Builds consider with clients and partners
Types of Cyber Security
Network Security
Network protection makes a special of protecting internal networks from intrusions, assaults and unauthorized get right of entry to. Firewall, intrusion detection systems and VPNs are common gear.
Application Security
Application protection entails securing software applications from vulnerabilities for the duration of improvement and after deployment. Regular updates and stable coding practices are crucial.
Cloud Security
With the rise of cloud computing, cyber safety in cloud environments has come to be essential. Cloud security protects records, workloads and packages hosted in cloud structures.
Endpoint Security
Endpoint protection protects devices along with laptops, mobile telephones and computer systems from cyber threats. Antivirus software program and endpoint detection equipment are widely used.
Data Security
Data security makes a special of protective data thru encryption, backups and get admission to manage mechanisms.
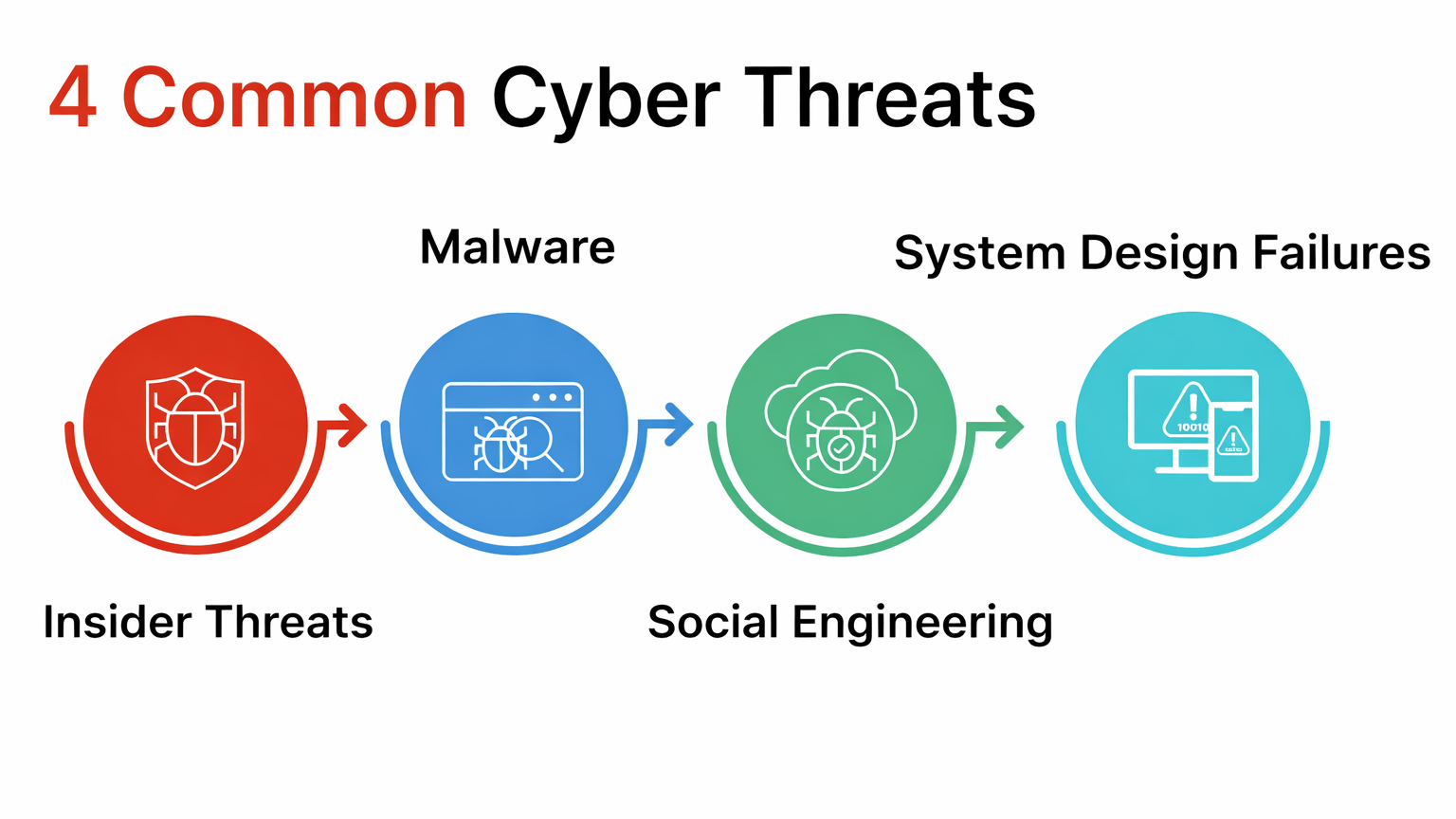
Common Cyber Security Threats
Some of the most not unusual cyber safety threats consist of:
- Malware and viruses
- Phishing assaults
- Ransomware
- Insider threat
- Distributed Denial of Service assault
Understanding those threats allows organizations reinforce their cyber protection defenses.
Key Benefit of Cyber Security
Data Protection
Cyber protection ensures that touchy commercial enterprise and purchaser facts stays safe from unauthorized get admission to.
Business Continuity
Strong cyber protection systems help save you downtime due to cyber assaults, maintaining operations jogging easily.
Regulatory Compliance
Data Protection enables groups comply with facts protection legal guidelines and enterprise rules.
Improved Customer Trust
Customers are much more likely to trust groups that prioritize cyber protection and statistics protection.
Cyber Security Trend Shaping the Future
AI Driven Cyber Security
Artificial Intelligence is transforming cyber safety by enabling actual time threat detection and automated responses.
Zero Trust Security
Zero Trust fashions expect no consumer or device is depended on by default, strengthening cyber safety frameworks.
Cloud Based Cyber Security
As cloud adoption grows, cloud local Data Protection solutions are getting more and more popular.
How Businesses Implement Cyber Security
Startups
Startups use Data Protection answers to protect highbrow assets and client facts whilst scaling operations.
Enterprises
Large corporations installation superior cyber protection systems for international hazard tracking, threat management, and compliance.
Remote Work Environments
Cyber safety enables steady faraway access via VPNs, identity control, and endpoint safety tools.
Challenges and Risk in Cyber Security
Evolve Threat Landscape
Cyber threat continuously evolve, making Data Protection a non stop challenge.
Skill Shortage
There is a global shortage of skilled Data Protection expert.
High Implementation Cost
Advanced cyber security solution may be costly for small businesses.
Best Practice for Cyber Security
- Conduct regular safety audit
- Use strong authentication methods
- Train employ on Data Protection cognizance
- Implement data encryption and backup
- Monitor systems constantly

Strong cybersecurity is important for businesses today. AI tools and multi-layered firewalls help stop cyber threats.
Future Outlook Cyber Security in 2030
By 2030, cyber security might be deep incorporated with AI automation and quantum resistant encryption. Organizations will rely on predictive Data Protection systems to prevent attacks before they occur.
Conclusion
Cyber protection is no longer non compulsory inside the current digital economy. It protects information, guarantees commercial enterprise continuity, and builds patron trust. Organizations that invest in strong cyber safety strategies today will be better organized to face destiny virtual threats and continue to be competitive.